
As the Russian military grapples with Ukraine's long-awaited counter-offensive, the country's hackers have their eyes set on the UK.
Last week, the data of more than a hundred thousand Brits were stolen by cybercriminals calling themselves Klop, which in Russian means a blood-sucking bug.
A gang well known to cybersecurity researchers has raided major employers including British Airways, Boots and the BBC after exploiting a loophole in software used by a payroll provider.
The stolen information includes national insurance policy numbers and bank details.
The massive data breach follows a similar attack by a Russian-speaking hacker group on Capita and highlights how criminal cyber groups are stepping up attacks on the West under the watchful eye of Vladimir Putin.
The Five Eyes countries of America, Australia, the UK, Canada and New Zealand have warned that «cybercrime groups linked to Russia» are threatening to «conduct cyber operations» against the West in retaliation for their actions. support for Ukraine.
Earlier this year, Cabinet Minister Oliver Dowden warned of a rise in «ideologically motivated» hackers who are increasingly attacking critical infrastructure and large businesses in an attempt to disrupt daily life.
0804 Cyberattacks on Russia
It is difficult to determine the degree of direction of these attacks by the Kremlin.
Rafe Pilling, director of intelligence at Secureworks, does not believe that Klop falls into the category of state-run Russian cyber gangs.
The group has a history of targeting Western businesses and extorting their data for money, suggesting that this week's attack is simply an extension of business as usual.
Putin, however, is at least tacitly encouraging such attacks, speaking out against the West in speeches and apparently tolerating hacker attacks launched from Russian soil.
Jeremy Kennelly, senior manager of the cybersecurity division of Google Cloud Mandiant, says that «historically, there has been some coordination between Russian cybercriminals and Russian government agencies.»
Researchers have noted an unusual coincidence between the activities of well-known Russian cyber gangs and military targets after the invasion of Ukraine. This relationship is reminiscent of the infamous “little green men” who took control of Crimea in 2014.
Putin denied that the heavily armed men in camouflage uniforms were Russian state operatives, arguing that they were simply well equipped. amateurs whose goals coincided with those of the Kremlin.
Now the little cyber helpers seem to play a similar role in the war in Ukraine.
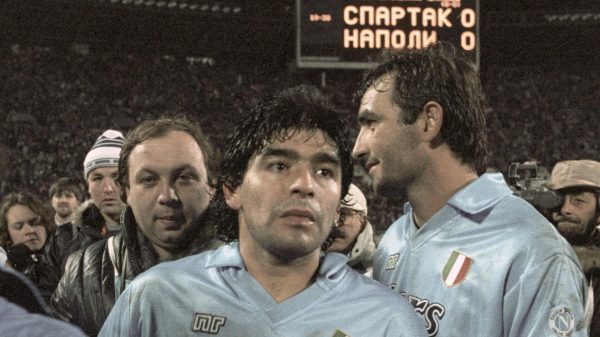
 Putin allowed hackers to operate with impunity from Russian territory. Photo: Getty Images Europe
Putin allowed hackers to operate with impunity from Russian territory. Photo: Getty Images Europe
Thanks to a series of arrests over the past two years, more is known about Clop members than many similar online criminal organizations.
The gang has been active for a decade and is believed to have extorted more than $500 million from corporate victims, including banks, airlines and law firms.
The FBI said last week that Clop «is considered one of the largest phishing and malicious spam providers in the world» and is believed to have compromised up to 8,000 companies worldwide.
“These are the oldest statesmen of Russian cybercrime,” says Pilling.
The group's goal is to steal data and then ransom it, threatening to leak sensitive information online if the money is not paid.
A typical ransom note reads: «If you ignore us, we will sell your information on the black market and publish it on our blog, which has 30-50 thousand unique visitors daily.»
In the case of BA, BBC and Boots, the gang discovered a vulnerability in file transfer software called MOVEit, which was used by payroll operator Zellis.
Pilling says it would take Bedbug «about 15-20 seconds» to go from finding a server with a backdoor to injecting data stealing software.
Google's Kennelly believes this latest spree may have given Bedbug more stolen information than its members can process.
In the past, the gang — or «threat» in cybersecurity industry jargon — contacted individual victims directly to demand money. However, this week, Klop instead posted a note on the dark web, ordering the hacked companies to contact him.
“The current situation is atypical,” explains Kennelly, “but may be due to actors being overwhelmed with access and data.” .
In a note posted on the dark web, Klop said: «If you are the government, city or police, don't worry, we have erased all your data.»
Pilling of Securworks believes this is a sign that Clop members fear the consequences of their actions: “I think they believe this announcement. enough to keep them off the radar of law enforcement and reduce the heat that will be directed at them.”
This is wishful thinking. Western officials are increasingly treating cyberattacks as a matter of national security, with the UK's National Cyber Security Center investigating the latest Clop attack.
Researchers say identifying Clop members is difficult because they even tend to stay away from cybercriminal forums, online message boards where criminals brag about their deeds and sell vast amounts of information stolen from Westerners.
However, it is believed that its operations are concentrated in Russia with some members in Ukraine.
 Ukrainian cyber police enter the house of a suspected Klop cyber gang member near Kiev , 2021 Photo: Police of Ukraine
Ukrainian cyber police enter the house of a suspected Klop cyber gang member near Kiev , 2021 Photo: Police of Ukraine
Police raids in Ukraine in the summer of 2021 and again in the weeks before Russia's 2022 invasion, however, lifted the veil of mystery over some alleged gang members and their lifestyles.
One suspect, a 36-year-old man, whose name is not called, lived in the capital of Ukraine Kiev with his wife. The photos released by Ukraine's Special Cyber Police show the couple living in a posh new home in a suburban area.
British and South Korean police were also present during the raid, having learned that the Bedbug targeted banks in their countries, although official sources are silent on what they learned during the raid.
< p> In June 2021, as a result of 21 similar raids six people were arrested.
 Cash and mobile phones seized by the Ukrainian police during a raid on the house of a suspected member of a cybergroup Photo: Police of Ukraine < p>Another home of the alleged perpetrator would not be out of place in the catalog of a prestigious British developer: black marble countertops, a 4-burner gas stove, fully equipped kitchen appliances and children's drawings glued to some kitchen cabinets.
Cash and mobile phones seized by the Ukrainian police during a raid on the house of a suspected member of a cybergroup Photo: Police of Ukraine < p>Another home of the alleged perpetrator would not be out of place in the catalog of a prestigious British developer: black marble countertops, a 4-burner gas stove, fully equipped kitchen appliances and children's drawings glued to some kitchen cabinets.
But among the home paraphernalia the police found several inches thick stacks of dollars, euros and Ukrainian banknotes hidden in safes and niches. Five million hryvnia (£108,000) was reportedly seized.
A $55,000 Tesla Model Y sedan was parked outside the house, and a silver Lexus parked outside was towed away, along with three Mercedes-Benzes, including a £183,000 S63 coupe.< /p>  Tesla Model Y worth $55,000 seized by police from Klop gang suspect Photo: Ukrainian Police
Tesla Model Y worth $55,000 seized by police from Klop gang suspect Photo: Ukrainian Police
Ukraine's cyber police said during the raid: «Six defendants were found to be attacking the servers of US and [South] Korean companies with malware such as ransomware.»
Experts. it is now believed that some of the people arrested in Ukraine were likely money launderers working on Klop's behalf rather than criminal hackers themselves, mainly because the arrests did not seem to slow down the ongoing crimes.
Even if the Bedbug can be eradicated, this will not solve the problem.
Western security and law enforcement agencies have long been disillusioned with Russia's tolerant attitude towards cybercriminals operating from its territory, with the multiplication of gangs.
Last year's report estimated that 74% of ransomware money in 2021 was paid to Russian-speaking hackers.
Joe Biden had a phone conversation with Putin to discuss how solve a hacking problem two years ago. However, any hope of a negotiated solution to the problem disappeared after the invasion.
Putin's little cyber assistants continue to rampage.


















































Свежие комментарии